Can Applocker Stop a Remote Code Exploit
This is the first in the series testing Applocker. Where it can provide protection, more importantly where it's weak and how to fix some of those weaknesses, well that's the plan.....
The tests will be carried out in isolation, all other security protections will be disabled. The only service protecting Windows from being pillaged is Applocker. Applocker's configuration is detailed here.
The details on how to run the EternalBlue attack from Metasploit are here.
The attacker is Kali on 10.1.1.100 running Eternal Blue.
The victim is Window 7 x64 on 10.1.1.106 with Applocker Enforced.
The EternalBlue exploit successfully launched against Windows 7 x64 with a remote Shell.

Whoami to shows I've System Privs

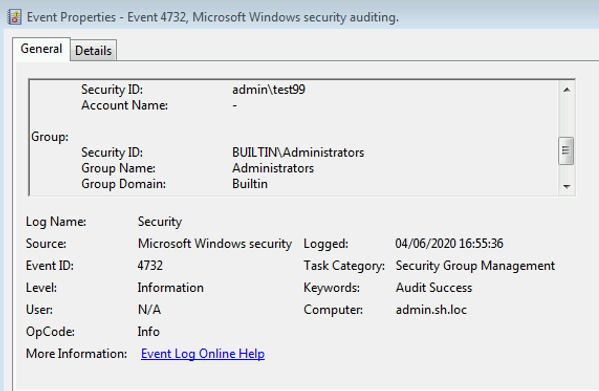
Next create a new local account and added to the local Administrators group. This is to test Applocker and Security Events logs.


The Security Events successfully logged the user create event and group add event, result.

A little disappointing is that Applocker did not create any logs as System, Nothing.
Conclusion
It's not surprising that Applocker did not prevent the exploit as it only protects the interactive users and does not prevent System or Service Accounts from running any programs or code.
It proves that security in isolation does not work and different layers of protection would have prevented this attack. It demonstrates that a SiEM (logging) is essential for the times the security controls fail, as long as the correct logging is configured.
